船過水無痕,時過境已遷。昔日容易事
,此刻恐難圓。
黑帽白帽因勢起︰
莊子、外篇『胠篋第十』上有一段文字︰
故 跖之徒問於跖曰:「盜亦有道乎?」跖曰:「何適而無有道邪? 妄意室中之藏,聖也;入先,勇也;出後,義也;知可否,知也;分均,仁也。五者不備而能成大盜者,天下未之有也。」由是觀之,善人不得聖人之道不立,跖不 得聖人之道不行;天下之善人少而不善人多,則聖人之利天下也少而害天下也多。
並有雜篇、盜跖第二十九一段故事,讀來令人津津有味,難道義賊廖添丁乃盜跖之傳人乎?東方的『大盜』哲學和西方的『駭客』觀點能否作比較呢?如果要比較,當然得知道 hacker 的源流。有位 Ben Yagoda 先生寫了一篇『 Hack 簡史』寫的很好。在此簡略的介紹,文中首先引用作者與美國方言學會會長談 “hack” 和 “hacker” 時的對話,會長說︰
the earliest examples share a relatively benign sense of “working on” a tech problem in a different, presumably more creative way than what’s outlined in an instruction manual.
也就是說最早所謂駭客是「創造性的使用說明書,用不一樣的辦法解決工程問題的人」。其後作者寫到,“hack” 一字 1955年就在 M.I.T 出現了,到了 1975 年 M.I.T 的電腦行話語詞表開啟了將 hacker 用於對電腦狂熱份子的宣言,並於所謂『八條定義』中開宗明義的說「駭客原指用大刀闊斧作傢俱的人」;其中第八條寫到︰
[deprecated] A malicious meddler who tries to discover sensitive information by poking around. Hence password hacker, network hacker. The correct term for this sense is cracker.
此條中〔勿用〕deprecated 一詞所說的『懷著惡意愛管閑事』者成了今天的黑帽駭客,或乾脆說黑客;相反的『本著活潑創造精神』者則變成今天的白帽駭客,也許簡稱為素客。同時作者論及駭客一詞的詞意變化、應用領域擴大…等等,於此就不多贅敘了。
─── 摘自《盜亦有道?》
,哪個不曾頭頂天?須知
滲透測試
滲透測試是指一個具備資安知識與經驗、技術人員受僱主所託,為僱主的網路設備、主機,模擬駭客的手法對網路或主機進行攻擊測試,為的是發掘系統漏洞、並提出改善方法,通常是出於善意
常用的工具如:nmap、Aircrack-NG、Wireshark
Penetration test
A penetration test, colloquially known as a pen test, is an authorized simulated attack on a computer system that looks for security weaknesses, potentially gaining access to the system’s features and data.[1][2]
The process typically identifies the target systems and a particular goal—then reviews available information and undertakes various means to attain the goal. A penetration test target may be a white box (which provides background and system information) or black box (which provides only basic or no information except the company name). A penetration test can help determine whether a system is vulnerable to attack, if the defenses were sufficient, and which defenses (if any) the test defeated.[3]
Security issues that the penetration test uncovers should be reported to the system owner.[4] Penetration test reports may also assess potential impacts to the organization and suggest countermeasures to reduce risk.[4]
The goals of a penetration test varies depending on the type of approved activity for any given engagement with the primary goal focused on finding vulnerabilities that could be exploited by a nefarious actor, and informing the client of those vulnerabilities along with recommended mitigation strategies.[5]
Penetration tests are a component of a full security audit. For example, the Payment Card Industry Data Security Standard requires penetration testing on a regular schedule, and after system changes.[6]
事,早就成現實!!趁著當下工具在??
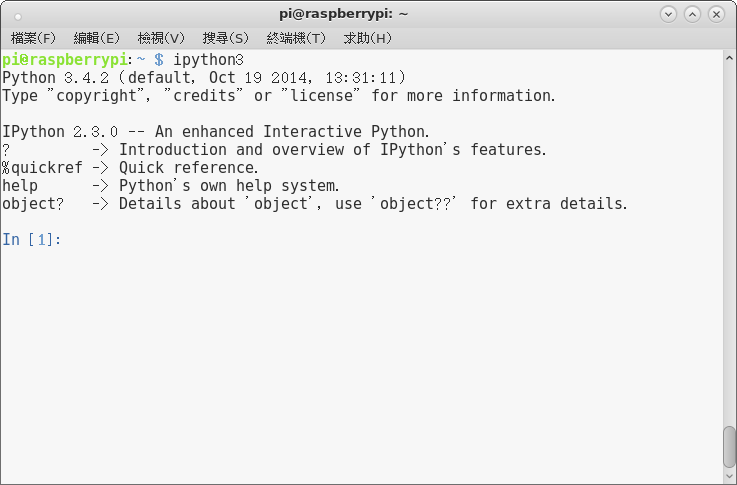
Kali Linux: Professional Penetration-Testing Distro
04. Kali Linux on ARM(20)
- Kali Linux – ASUS Chromebook Flip
- Kali Linux – MiniX
- Kali Linux – Cubietruck
- Kali Linux – Raspberry Pi2
- Kali Linux – Trimslice
- Kali Linux – Cubieboard2
- Kali Linux – RIoTboard
- Kali Linux – NanoPi2
- Kali Linux – Utilite Pro
- Kali Linux – ODROID-C1
- Kali Linux on USB Armory
- Kali Linux on Acer Tegra Chromebook 13″
- Kali Linux on ODROID-XU3
- Kali Linux – CuBox-i4Pro
- Kali Linux – Samsung Chromebook 2
探測資安乎☆
 Kali Linux
Kali Linux