一時想起派生的『非同步計算』架構建議
PEP 3148 — futures – execute computations asynchronously
Abstract
This PEP proposes a design for a package that facilitates the evaluation of callables using threads and processes.
Motivation
Python currently has powerful primitives to construct multi-threaded and multi-process applications but parallelizing simple operations requires a lot of work i.e. explicitly launching processes/threads, constructing a work/results queue, and waiting for completion or some other termination condition (e.g. failure, timeout). It is also difficult to design an application with a global process/thread limit when each component invents its own parallel execution strategy.
───
,以及『 SCOOP 』 Python 『分佈式』可擴張『並行運算』平台,
SCOOP (Scalable COncurrent Operations in Python) is a distributed task module allowing concurrent parallel programming on various environments, from heterogeneous grids to supercomputers.
Philosophy
Our philosophy is based on these ideas:
- The future is parallel;
- Simple is beautiful;
- Parallelism should be simpler.
These tenets are translated concretely in a minimum number of functions allowing maximum parallel efficiency while keeping at minimum the inner knowledge required to use them. It is implemented with Python 3 in mind while being compatible with 2.6+ to allow fast prototyping without sacrificing efficiency and speed.
Features
SCOOP has many features and advantages over Futures, multiprocessing and similar modules, such as:
- Harness the power of multiple computers over network;
- Ability to spawn subtasks within tasks;
- API compatible with PEP 3148;
- Parallelizing serial programs with only minor modifications;
- Efficient load-balancing.
Anatomy of a SCOOPed program
SCOOP can handle multiple diversified multi-layered tasks. You can submit your different functions and data simultaneously and effortlessly while the framework executes them locally or remotely. Contrarily to most multiprocessing frameworks, it allows to launch subtasks within tasks.
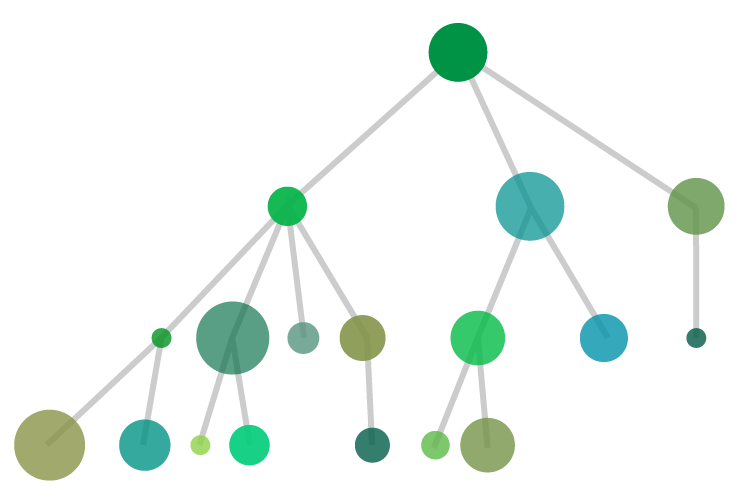 Through SCOOP, you can simultaneously execute tasks that are of different nature (Discs of different colors) or different by complexity (Discs radiuses). The module will handle the physical considerations of parallelization such as task distribution over your resources (load balancing), communications, etc.
Through SCOOP, you can simultaneously execute tasks that are of different nature (Discs of different colors) or different by complexity (Discs radiuses). The module will handle the physical considerations of parallelization such as task distribution over your resources (load balancing), communications, etc.
Applications
The common applications of SCOOP consist of, but is not limited to:
- Evolutionary Algorithms
- Monte Carlo simulations
- Data mining
- Data processing
- I/O processing
- Graph traversal
───
也許如是方能將『一萬臺樹莓派』給組織起來,真可以同時協作的吧?畢竟根本不知那『 It 網』的構造方式原理,即使想問也不知該從何問起的哩!
─── 《勇闖新世界︰ W!O《卡夫卡村》變形祭︰感知自然‧尖端‧六上》
xkcd/936 上的簡短漫畫︰

A webcomic of romance,
sarcasm, math, and language.
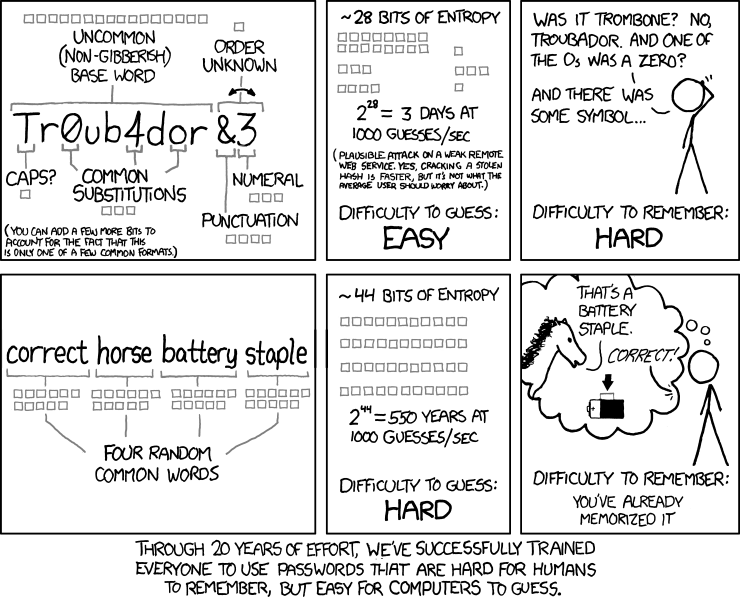
笑話人『難』記,電腦『易』猜之『密碼』?
俗話說︰時間即金錢。
恰是那個『難』『易』的『尺度』哩!
切莫以此為『心』『安』!?
怎知『劊客』他不擅長『讀心術』呢?!
root@kali:~/test# unshadow /etc/passwd /etc/shadow > passwords.txt root@kali:~/test# john passwords.txt Created directory: /root/.john Using default input encoding: UTF-8 Loaded 1 password hash (sha512crypt, crypt(3)[SHA512 64/32 OpenSSL]) Press 'q' or Ctrl-C to abort, almost any other key for status toor (root) 1g 0:00:00:00 DONE 1/3 (2018-10-26 08:45) 4.761g/s 33.33p/s 33.33c/s 33.33C/s toor Use the "--show" option to display all of the cracked passwords reliably Session completed root@kali:~/test# john --show passwords.txt root:toor:0:0:root:/root:/bin/bash 1 password hash cracked, 0 left
※ 註︰
John the Ripper’s cracking modes.
“Single crack” mode.
This is the mode you should start cracking with. It will use the login names, “GECOS” / “Full Name” fields, and users’ home directory names as candidate passwords, also with a large set of mangling rules applied. Since the information is only used against passwords for the accounts it was taken from (and against password hashes which happened to be assigned the same salt), “single crack” mode is much faster than wordlist mode. This permits for the use of a much larger set of word mangling rules with “single crack”, and their use is always enabled with this mode. Successfully guessed passwords are also tried against all loaded password hashes just in case more users have the same password.
Note that running this mode on many password files simultaneously may sometimes get more passwords cracked than it would if you ran it on the individual password files separately.
萬一他還有 SCoOP 組成之『超級電腦』網絡,又精通『資料探勘』耶☻
THE SPRAWL
projects password analysis and cracking kit
| Download | PACK-0.0.4.tar.gz |
|---|---|
| Size | 68.8 KB |
| Date | August 8th, 2013 |
| Version | 0.0.4 |
PACK (Password Analysis and Cracking Toolkit) is a collection of utilities developed to aid in analysis of password lists in order to enhance password cracking through pattern detection of masks, rules, character-sets and other password characteristics. The toolkit generates valid input files for Hashcat family of password crackers.
NOTE: The toolkit itself is not able to crack passwords, but instead designed to make operation of password crackers more efficient.
Table of Contents
Selecting passwords lists for analysis
Before we can begin using the toolkit we must establish a selection criteria of password lists. Since we are looking to analyze the way people create their passwords, we must obtain as large of a sample of leaked passwords as possible. One such excellent list is based on RockYou.com compromise. This list both provides large and diverse enough collection that provides a good results for common passwords used by similar sites (e.g. social networking). The analysis obtained from this list may not work for organizations with specific password policies. As such, selecting sample input should be as close to your target as possible. In addition, try to avoid obtaining lists based on already cracked passwords as it will generate statistics bias of rules and masks used by individual(s) cracking the list and not actual users.
問『鹿』死誰手?眼下結果不分明呦★
StatsGen
The most basic analysis that you can perform is simply obtaining most common length, character-set and other characteristics of passwords in the provided list. In the example below, we will use ‘rockyou.txt’ containing approximately 14 million passwords. Launch statsgen.pywith the following command line:
$ python statsgen.py rockyou.txt
Below is the output from the above command:
root@kali:~/test# statsgen rockyou.txt
_
StatsGen 0.0.3 | |
_ __ __ _ ___| | _
| '_ \ / _` |/ __| |/ /
| |_) | (_| | (__| <
| .__/ \__,_|\___|_|\_\
| |
|_| iphelix@thesprawl.org
[*] Analyzing passwords in [rockyou.txt]
[+] Analyzing 100% (14344391/14344391) of passwords
NOTE: Statistics below is relative to the number of analyzed passwords, not total number of passwords
[*] Length:
[+] 8: 20% (2966037)
[+] 7: 17% (2506271)
[+] 9: 15% (2191040)
[+] 10: 14% (2013695)
[+] 6: 13% (1947798)
[+] 11: 06% (866035)
[+] 12: 03% (555350)
[+] 13: 02% (364174)
[+] 5: 01% (259169)
[+] 14: 01% (248527)
[+] 15: 01% (161213)
[+] 16: 00% (118406)
[+] 17: 00% (36884)
[+] 18: 00% (23769)
[+] 4: 00% (17899)
[+] 19: 00% (15567)
[+] 20: 00% (13069)
[+] 21: 00% (7850)
[+] 22: 00% (6156)
[+] 23: 00% (4849)
[+] 24: 00% (4237)
[+] 25: 00% (2950)
[+] 3: 00% (2461)
[+] 26: 00% (2249)
[+] 27: 00% (1811)
[+] 28: 00% (1198)
[+] 30: 00% (992)
[+] 29: 00% (785)
[+] 255: 00% (476)
[+] 31: 00% (469)
[+] 32: 00% (407)
[+] 2: 00% (335)
[+] 33: 00% (296)
[+] 34: 00% (193)
[+] 36: 00% (188)
[+] 35: 00% (131)
[+] 39: 00% (118)
[+] 37: 00% (81)
[+] 42: 00% (81)
[+] 38: 00% (67)
[+] 45: 00% (56)
[+] 40: 00% (55)
[+] 41: 00% (46)
[+] 1: 00% (45)
[+] 71: 00% (45)
[+] 43: 00% (43)
[+] 48: 00% (40)
[+] 44: 00% (31)
[+] 55: 00% (28)
[+] 54: 00% (27)
[+] 50: 00% (26)
[+] 46: 00% (25)
[+] 47: 00% (23)
[+] 69: 00% (23)
[+] 51: 00% (22)
[+] 61: 00% (21)
[+] 60: 00% (20)
[+] 49: 00% (18)
[+] 58: 00% (18)
[+] 56: 00% (17)
[+] 57: 00% (17)
[+] 64: 00% (17)
[+] 52: 00% (16)
[+] 53: 00% (16)
[+] 63: 00% (16)
[+] 70: 00% (16)
[+] 222: 00% (15)
[+] 66: 00% (12)
[+] 67: 00% (12)
[+] 74: 00% (12)
[+] 75: 00% (11)
[+] 59: 00% (9)
[+] 84: 00% (9)
[+] 62: 00% (8)
[+] 68: 00% (8)
[+] 72: 00% (8)
[+] 65: 00% (7)
[+] 73: 00% (7)
[+] 80: 00% (7)
[+] 76: 00% (6)
[+] 79: 00% (6)
[+] 81: 00% (6)
[+] 101: 00% (6)
[+] 246: 00% (6)
[+] 78: 00% (5)
[+] 87: 00% (5)
[+] 210: 00% (5)
[+] 219: 00% (5)
[+] 77: 00% (4)
[+] 82: 00% (4)
[+] 85: 00% (4)
[+] 88: 00% (4)
[+] 96: 00% (4)
[+] 117: 00% (4)
[+] 129: 00% (4)
[+] 150: 00% (4)
[+] 221: 00% (4)
[+] 83: 00% (3)
[+] 91: 00% (3)
[+] 94: 00% (3)
[+] 95: 00% (3)
[+] 108: 00% (3)
[+] 125: 00% (3)
[+] 142: 00% (3)
[+] 146: 00% (3)
[+] 165: 00% (3)
[+] 188: 00% (3)
[+] 220: 00% (3)
[+] 224: 00% (3)
[+] 232: 00% (3)
[+] 243: 00% (3)
[+] 90: 00% (2)
[+] 92: 00% (2)
[+] 98: 00% (2)
[+] 102: 00% (2)
[+] 103: 00% (2)
[+] 104: 00% (2)
[+] 109: 00% (2)
[+] 111: 00% (2)
[+] 113: 00% (2)
[+] 123: 00% (2)
[+] 124: 00% (2)
[+] 134: 00% (2)
[+] 154: 00% (2)
[+] 173: 00% (2)
[+] 178: 00% (2)
[+] 182: 00% (2)
[+] 190: 00% (2)
[+] 194: 00% (2)
[+] 195: 00% (2)
[+] 197: 00% (2)
[+] 207: 00% (2)
[+] 208: 00% (2)
[+] 216: 00% (2)
[+] 217: 00% (2)
[+] 218: 00% (2)
[+] 225: 00% (2)
[+] 226: 00% (2)
[+] 228: 00% (2)
[+] 237: 00% (2)
[+] 238: 00% (2)
[+] 239: 00% (2)
[+] 241: 00% (2)
[+] 249: 00% (2)
[+] 254: 00% (2)
[+] 257: 00% (2)
[+] 262: 00% (2)
[+] 86: 00% (1)
[+] 89: 00% (1)
[+] 93: 00% (1)
[+] 97: 00% (1)
[+] 99: 00% (1)
[+] 100: 00% (1)
[+] 105: 00% (1)
[+] 106: 00% (1)
[+] 115: 00% (1)
[+] 118: 00% (1)
[+] 126: 00% (1)
[+] 131: 00% (1)
[+] 132: 00% (1)
[+] 133: 00% (1)
[+] 137: 00% (1)
[+] 138: 00% (1)
[+] 141: 00% (1)
[+] 145: 00% (1)
[+] 148: 00% (1)
[+] 149: 00% (1)
[+] 151: 00% (1)
[+] 153: 00% (1)
[+] 162: 00% (1)
[+] 168: 00% (1)
[+] 170: 00% (1)
[+] 171: 00% (1)
[+] 172: 00% (1)
[+] 174: 00% (1)
[+] 175: 00% (1)
[+] 176: 00% (1)
[+] 184: 00% (1)
[+] 189: 00% (1)
[+] 192: 00% (1)
[+] 198: 00% (1)
[+] 200: 00% (1)
[+] 202: 00% (1)
[+] 203: 00% (1)
[+] 204: 00% (1)
[+] 206: 00% (1)
[+] 209: 00% (1)
[+] 211: 00% (1)
[+] 213: 00% (1)
[+] 230: 00% (1)
[+] 231: 00% (1)
[+] 233: 00% (1)
[+] 234: 00% (1)
[+] 240: 00% (1)
[+] 242: 00% (1)
[+] 244: 00% (1)
[+] 245: 00% (1)
[+] 248: 00% (1)
[+] 251: 00% (1)
[+] 252: 00% (1)
[+] 258: 00% (1)
[+] 266: 00% (1)
[+] 285: 00% (1)
[*] Character-set:
[+] loweralphanum: 42% (6074867)
[+] loweralpha: 25% (3726129)
[+] numeric: 16% (2346744)
[+] loweralphaspecialnum: 02% (426353)
[+] upperalphanum: 02% (407431)
[+] mixedalphanum: 02% (382237)
[+] loweralphaspecial: 02% (381623)
[+] upperalpha: 01% (229875)
[+] mixedalpha: 01% (159310)
[+] all: 00% (53238)
[+] mixedalphaspecial: 00% (49655)
[+] specialnum: 00% (46606)
[+] upperalphaspecialnum: 00% (27737)
[+] upperalphaspecial: 00% (26813)
[+] special: 00% (5773)
[*] Password complexity:
[+] digit: min(0) max(255)
[+] lower: min(0) max(255)
[+] upper: min(0) max(187)
[+] special: min(0) max(255)
[*] Simple Masks:
[+] stringdigit: 37% (5339556)
[+] string: 28% (4115314)
[+] digit: 16% (2346744)
[+] digitstring: 04% (663951)
[+] othermask: 04% (576325)
[+] stringdigitstring: 03% (450742)
[+] stringspecialstring: 01% (204441)
[+] stringspecialdigit: 01% (167816)
[+] stringspecial: 01% (148328)
[+] digitstringdigit: 00% (130517)
[+] stringdigitspecial: 00% (77378)
[+] specialstringspecial: 00% (25127)
[+] digitspecialstring: 00% (16821)
[+] specialstring: 00% (14496)
[+] digitstringspecial: 00% (12242)
[+] digitspecialdigit: 00% (12114)
[+] digitspecial: 00% (11017)
[+] specialstringdigit: 00% (9609)
[+] specialdigitstring: 00% (8328)
[+] special: 00% (5773)
[+] specialdigit: 00% (4142)
[+] specialdigitspecial: 00% (3610)
[*] Advanced Masks:
[+] ?l?l?l?l?l?l?l?l: 04% (687991)
[+] ?l?l?l?l?l?l: 04% (601152)
[+] ?l?l?l?l?l?l?l: 04% (585013)
[+] ?l?l?l?l?l?l?l?l?l: 03% (516830)
[+] ?d?d?d?d?d?d?d: 03% (487429)
[+] ?d?d?d?d?d?d?d?d?d?d: 03% (478196)
[+] ?d?d?d?d?d?d?d?d: 02% (428296)
[+] ?l?l?l?l?l?l?d?d: 02% (420318)
[+] ?l?l?l?l?l?l?l?l?l?l: 02% (416939)
[+] ?d?d?d?d?d?d: 02% (390529)
[+] ?d?d?d?d?d?d?d?d?d: 02% (307532)
[+] ?l?l?l?l?l?d?d: 02% (292306)
[+] ?l?l?l?l?l?l?l?d?d: 01% (273624)
[+] ?l?l?l?l?l?l?l?l?l?l?l: 01% (267733)
[+] ?l?l?l?l?d?d?d?d: 01% (235360)
[+] ?l?l?l?l?d?d: 01% (215074)
[+] ?l?l?l?l?l?l?l?l?d?d: 01% (213109)
[+] ?l?l?l?l?l?l?d: 01% (193097)
[+] ?l?l?l?l?l?l?l?d: 01% (189847)
[+] ?l?l?l?l?l?l?l?l?l?l?l?l: 01% (189355)
[+] ?l?l?l?d?d?d?d: 01% (178304)
[+] ?l?l?l?l?l?d?d?d?d: 01% (173559)
[+] ?l?l?l?l?l?l?d?d?d?d: 01% (160592)
[+] ?l?l?l?l?l?l?l?l?d: 01% (160054)
[+] ?l?l?l?l?l?d?d?d: 01% (152400)